The Page 33 Problem
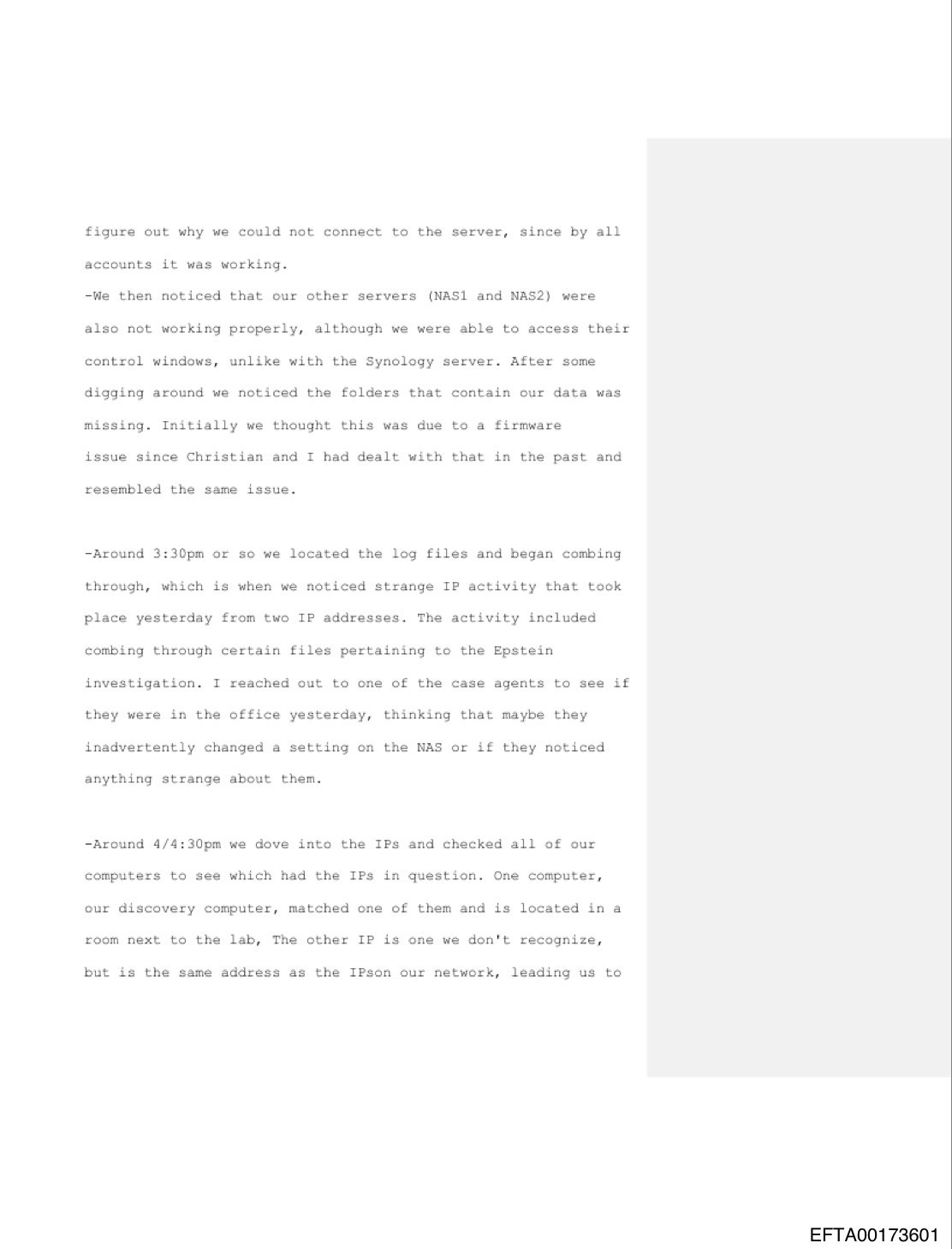
Buried deep inside EFTA00173569 is a passage that deserves careful reading because it shifts the focus away from personalities and toward infrastructure. On page 33, an FBI-affiliated digital forensics specialist describes reviewing network logs connected to a storage environment used in investigative work. During that review, he documents IP activity he considered unusual and explains that the behavior appeared to involve someone “combing through certain files pertaining to the Epstein investigation.”
In technical environments like this, access patterns are rarely ambiguous. Investigative storage systems are permissioned, logged, segmented, and routinely monitored. Analysts understand what normal looks like: scheduled pulls, assigned case access, structured retrieval tied to specific tasks. When an experienced digital examiner pauses long enough to describe activity as irregular, that reflects deviation from expected workflow rather than casual browsing. The phrasing in the affidavit indicates that the review was not incidental system noise but a sequence of activity directed toward Epstein-related materials, observed in a way that triggered concern rather than routine documentation.
The significance lies in what the document quietly implies about process. Sensitive investigations depend on strict digital evidence governance. Authentication trails, device attribution, timestamp reconciliation, and supervisory authorization exist precisely to prevent untracked access or exploratory review detached from formal tasking. If internal personnel were identifying IP activity that required explanation, then there should also exist corresponding incident analysis, follow-up documentation, and formal determination about whether the access was authorized, misconfigured, or improper. That paper trail matters more than any individual claim in isolation because it speaks to whether the evidence environment was as controlled as the public has been led to believe.
This is not about dramatizing a line in a report but about understanding what digital custody actually requires. The Epstein investigation has generated years of public debate centered on names and narratives. Page 33 directs attention somewhere more fundamental: the technical perimeter where evidence lives, moves, and is safeguarded. If that perimeter showed signs of irregular access, even briefly, then the integrity conversation expands beyond testimony and into system governance.
Readers who care about accountability should not skim that page. It identifies a point where internal technical observation intersected with a case of extraordinary public consequence. Whether the anomaly was resolved, dismissed, or escalated is a matter that deserves scrutiny. The document itself confirms that the anomaly existed and was serious enough to record in sworn form.